The Exploding Attack Surface: IT/OT Convergence & IoT Vulnerabilities
The rapid deployment of connected assets—from UHF RFID tags on pallets to smart sensors on machinery and autonomous vehicles—has created an expansive and complex cyber attack surface. Each new device represents a potential entry point for malicious actors. This challenge is further compounded by the accelerating convergence of Information Technology (IT) and Operational Technology (OT) networks. Historically, OT environments in manufacturing plants, logistics hubs, and healthcare facilities operated in isolated silos, but modern asset tracking demands seamless data flow across these domains. This convergence exposes traditionally air-gapped critical systems to IT-borne threats, making them vulnerable to ransomware, industrial espionage, and operational disruption. A compromised UHF RFID reader on a loading dock, for example, could be a gateway for an attacker to pivot into a broader OT network, impacting production or disrupting supply chains. The sheer volume and diversity of these devices make traditional perimeter-based security models obsolete. Organizations must undertake comprehensive asset inventory and risk assessments that span both IT and OT environments, prioritizing critical assets based on their potential business impact (CSO Online, 2024).

New Frontiers of Threat: AI-Powered Exploits and Supply Chain Attacks
Beyond traditional malware, the cybersecurity landscape in 2025 will be dominated by increasingly sophisticated and AI-powered threats. Adversarial AI, for instance, could be used to manipulate sensor data, leading to misreported inventory from UHF RFID reads or erroneous machine performance metrics, causing significant operational and financial damage. Deepfakes could bypass biometric authentication systems, compromising access to secure facilities or critical digital platforms. Ransomware is also evolving, with sophisticated variants specifically targeting OT environments, often employing 'double extortion' tactics: encrypting critical systems and exfiltrating sensitive data, then demanding payment for both decryption and to prevent data leaks (SC Magazine, 2024). Furthermore, supply chain attacks pose a severe and growing risk. Vulnerabilities introduced during the manufacturing of IoT devices or software components, such as a compromised firmware update for an RFID gateway, can create systemic weaknesses across an entire asset tracking infrastructure. This means the security of your connected assets is only as strong as its weakest link, often found deep within the supply chain. To mitigate this, organizations must implement rigorous vendor risk management programs, demand Software Bill of Materials (SBOMs) from all suppliers, and scrutinize the security posture of every partner involved in their asset tracking ecosystem. The escalating demand for robust security solutions against these threats is evident in market projections: the global IoT security market, valued at approximately USD 17.1 billion in 2023, is forecast to reach USD 75.4 billion by 2030, exhibiting a Compound Annual Growth Rate (CAGR) of 23.6% (MarketsandMarkets, 2024).

Zero Trust and Edge Security: Foundations for Resilient Asset Tracking
The dynamic, distributed nature of IoT asset management renders traditional perimeter security inadequate. A Zero Trust Architecture (ZTA)—operating on the principle of 'never trust, always verify'—becomes not just an advantage but an imperative. This model mandates continuous authentication and authorization for every device (from individual UHF RFID tags to powerful gateways), user, and application attempting to access network resources, regardless of its location. Implementing ZTA involves micro-segmentation, which isolates individual assets or groups of similar assets into small, distinct network segments, drastically limiting the lateral movement of threats in case of a breach. Strong multi-factor authentication and granular, least-privilege access controls are essential for all connected assets and their users. Concurrently, securing the 'edge' is paramount. As more data processing and decision-making shift closer to the source—think smart sensors, intelligent RFID readers, and local gateways—these physically exposed and often resource-constrained devices become critical entry points for attackers. Edge vulnerabilities can be exploited to gain access to broader networks. Effective edge security requires deploying hardware-level security features like Hardware Root of Trust (HRoT) and Secure Boot, ensuring only authenticated and authorized firmware can run. Robust encryption for data at rest and in transit, combined with secure, cryptographically signed Over-the-Air (OTA) firmware updates, are non-negotiable for safeguarding these vital components of your asset tracking system (ZDNet, 2024).

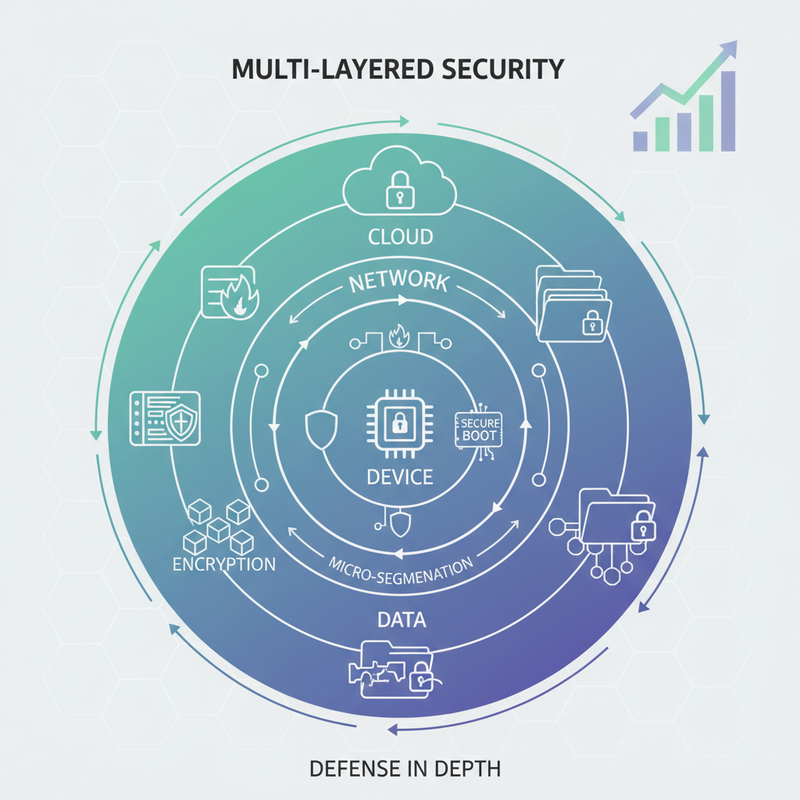
A Multi-Layered Defense: Technical Solutions for Connected Assets
Securing connected assets in 2025 demands a multi-layered, holistic approach that addresses every component of the ecosystem. At the **device level**, implementing Hardware Root of Trust (HRoT) and Secure Boot ensures that only trusted firmware operates, while Trusted Platform Modules (TPMs) or Secure Elements (SEs) provide secure storage for cryptographic keys and unique device identities. Cryptographically signed and encrypted Over-The-Air (OTA) firmware updates, with rollback protection, are crucial for maintaining device integrity throughout its lifecycle. Each asset, including UHF RFID readers and specialized tags, should possess a unique digital identity (e.g., X.509 certificates) for mutual authentication. **Network security** relies on micro-segmentation to prevent lateral threat movement and Zero Trust Network Access (ZTNA) for granular, context-aware access control. Specialized Intrusion Detection/Prevention Systems (IDPS) are vital for monitoring IoT/OT network traffic for anomalies, while secure connectivity protocols (TLS/SSL, IPsec) encrypt data in transit. For **data security**, encryption at rest and in transit is fundamental for all sensitive asset tracking information. Data minimization, anonymization, and cryptographic hashing ensure data integrity and non-repudiation—critical for verifying the authenticity of RFID scan logs and sensor readings. Emerging applications of Blockchain/DLT are also providing immutable records for asset provenance and enhanced auditability (MarketsandMarkets, 2024). Finally, **cloud and platform security** protects the central nervous system of your asset management system. This includes securing APIs that integrate devices with backend platforms, employing Cloud Security Posture Management (CSPM) for continuous configuration monitoring, and robust Identity and Access Management (IAM) for both users and connected devices.
Proactive Monitoring and Regulatory Drive for "Secure-by-Design"
Effective cybersecurity for connected assets extends beyond initial deployment; it requires continuous vigilance. AI and Machine Learning (AI/ML)-driven behavioral analytics and anomaly detection are indispensable for establishing 'normal' operational baselines for asset behavior. These systems can quickly flag deviations—such as unusual RFID read patterns, unexpected device communications, or abnormal sensor readings—that might indicate a cyber attack. Centralized logging, coupled with Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) systems, aggregates data from all connected assets, gateways, and cloud platforms. This allows for rapid correlation of events, automated threat hunting, and streamlined incident response. Beyond active monitoring, organizations face increasing regulatory pressure to embed security from the ground up. Forthcoming regulations like the EU Cyber Resilience Act (CRA) are set to mandate 'secure-by-design' principles for connected devices, placing significant responsibility on manufacturers and deployers for the entire product lifecycle (European Commission, 2022). Compliance will shift from an afterthought to a foundational requirement, impacting procurement and development processes. Proactively integrating security requirements into the design and procurement of all new connected assets, ensuring vendor adherence to emerging cybersecurity standards (such as NIST frameworks), is no longer optional but a strategic imperative (NIST Publications).

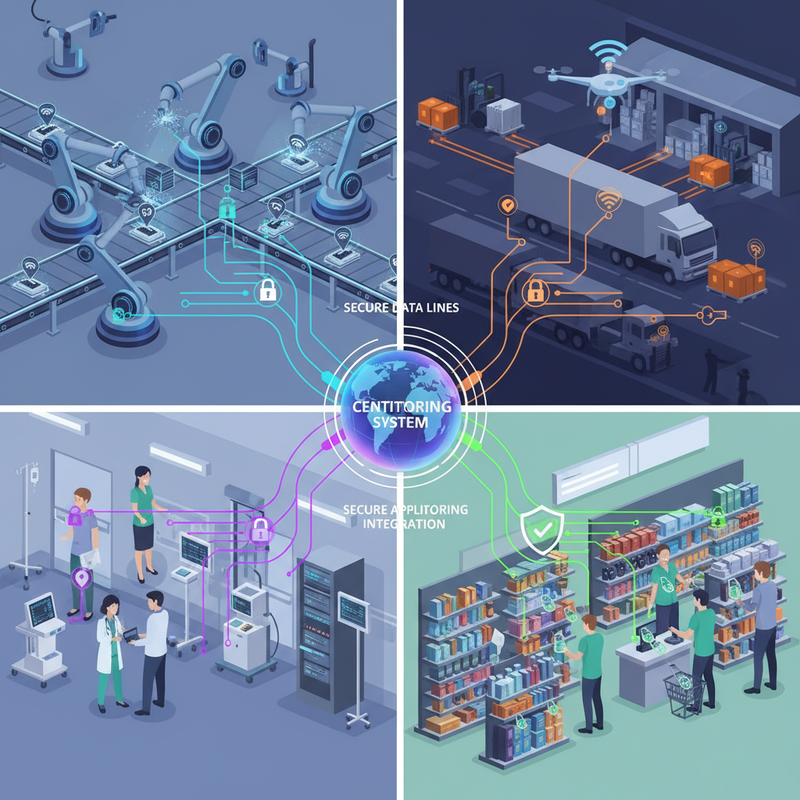
Industry Applications: Securing Asset Tracking in Action
The principles of cybersecurity for connected assets are critical across diverse industries utilizing UHF RFID and other IoT technologies: In **Manufacturing & Industrial IoT (IIoT)**, an automotive manufacturer might use secured IoT sensors and RFID tags to track components across its global supply chain and within smart factories. Network segmentation isolates critical OT systems (like PLCs and robotic arms), preventing ransomware from spreading from IT to production lines. AI-driven anomaly detection monitors machine performance for predictive maintenance and potential cyber tampering. Zero Trust ensures only authorized systems can communicate with specific control points. For **Logistics & Supply Chain Management**, a pharmaceutical company leverages IoT-enabled temperature and location trackers for its cold chain. End-to-end encryption secures data from sensors and RFID readers to the cloud, with secure boot protecting each device. Digital signatures verify asset integrity during transit, mitigating theft and ensuring regulatory compliance. Blockchain technology is actively being explored to provide an immutable audit trail of product provenance. **Healthcare Asset Tracking** deploys Wi-Fi and Bluetooth Low Energy (BLE) trackers for medical equipment (e.g., IV pumps, wheelchairs) and patient monitoring devices. These IoMT systems are secured with device identity certificates, strong Role-Based Access Controls (RBAC), and network segmentation to isolate them from the main hospital network. Continuous monitoring detects unauthorized device behavior, crucial for HIPAA compliance and patient safety. In **Retail & Inventory Management**, UHF RFID tags and readers are instrumental for real-time inventory. Security focuses on protecting reader networks from unauthorized access and ensuring data integrity between readers and backend inventory systems. Secure API gateways prevent malicious manipulation of inventory counts, safeguarding revenue and operational efficiency.
Conclusion
The interconnected world of asset tracking, powered by technologies like UHF RFID, offers immense benefits but demands an unyielding commitment to cybersecurity. The evolving threat landscape, marked by AI-powered attacks and pervasive supply chain vulnerabilities, necessitates a strategic, multi-layered defense. Embracing Zero Trust, securing the edge, integrating 'secure-by-design' principles, and continuous monitoring are no longer options but imperatives for maintaining operational integrity and protecting valuable assets. Is your asset tracking infrastructure truly secure for 2025 and beyond? Contact Tag N Trak It today to assess your vulnerabilities and build a resilient, future-proof asset management security strategy.
- RFID and IoT security best practices to follow in 2024
- IoT asset management: Cybersecurity trends to watch
- Securing the IoT edge for asset tracking: A comprehensive guide
- IoT Security Market - Global Forecast to 2030
- Proposal for a Regulation on horizontal cybersecurity requirements for products with digital elements (Cyber Resilience Act)
- NIST IoT Cybersecurity Program
